Best Cisco 210-260 pdf exam study materials are written according to the latest real IT exams. All the Cisco 210-260 exam practice questions and answers are revised by the skillful experts. http://www.leads4pass.com/210-260.html 100% success and guarantee to pass 210-260 exam test quickly and easily at first attempt.
QUESTION 1
How does a device on a network using ISE receive its digital certificate during the new- device registration process?
A. ISE acts as a SCEP proxy to enable the device to receive a certificate from a central CA server.
B. ISE issues a certificate from its internal CA server.
C. ISE issues a pre-defined certificate from a local database.
D. The device requests a new certificate directly from a central CA.
Correct Answer: A
QUESTION 2
Refer to the exhibit.
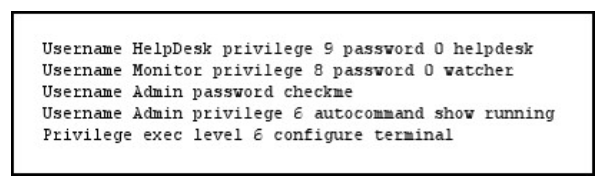
The Admin user is unable to enter configuration mode on a device with the given configuration. What change can you make to the configuration to correct the problem?
A. Remove the autocommand keyword and arguments from the username admin privilege line.
B. Change the Privilege exec level value to 15.
C. Remove the two Username Admin lines.
D. Remove the Privilege exec line.
Correct Answer: A
QUESTION 3
When an administrator initiates a device wipe command from the ISE, what is the immediate effect?
A. It requests the administrator to choose between erasing all device data or only managed corporate data.
B. It requests the administrator to enter the device PIN or password before proceeding with the operation.
C. It notifies the device user and proceeds with the erase operation.
D. It immediately erases all data on the device.
Correct Answer: A
QUESTION 4
You have implemented a Sourcefire IPS and configured it to block certain addresses utilizing Security Intelligence IP Address Reputation. A user calls and is not able to access a certain IP address. What action can you take to allow the user access to the IP address?
A. Create a whitelist and add the appropriate IP address to allow the traffic.
B. Create a custom blacklist to allow the traffic.
C. Create a user based access control rule to allow the traffic.
D. Create a network based access control rule to allow the traffic.
E. Create a rule to bypass inspection to allow the traffic.
Correct Answer: A
QUESTION 5
What is a benefit of a web application firewall?
A. It blocks known vulnerabilities without patching applications.
B. It simplifies troubleshooting.
C. It accelerates web traffic.
D. It supports all networking protocols.
Correct Answer: A
QUESTION 6
Refer to the exhibit.
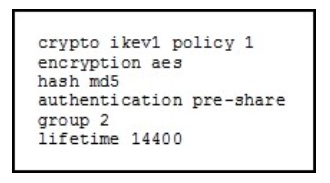
What is the effect of the given command sequence?
A. It configures IKE Phase 1.
B. It configures a site-to-site VPN tunnel.
C. It configures a crypto policy with a key size of 14400.
D. It configures IPSec Phase 2.
Correct Answer: A
QUESTION 7
What are purposes of the Internet Key Exchange in an IPsec VPN? (Choose two.)
A. The Internet Key Exchange protocol establishes security associations
B. The Internet Key Exchange protocol provides data confidentiality
C. The Internet Key Exchange protocol provides replay detection
D. The Internet Key Exchange protocol is responsible for mutual authentication
Correct Answer: AD
QUESTION 8
Which statements about smart tunnels on a Cisco firewall are true? (Choose two.)
A. Smart tunnels can be used by clients that do not have administrator privileges
B. Smart tunnels support all operating systems
C. Smart tunnels offer better performance than port forwarding
D. Smart tunnels require the client to have the application installed locally
Correct Answer: AC
QUESTION 9
What is the best way to confirm that AAA authentication is working properly?
A. Use the test aaa command.
B. Ping the NAS to confirm connectivity.
C. Use the Cisco-recommended configuration for AAA authentication.
D. Log into and out of the router, and then check the NAS authentication log.
Correct Answer: A
QUESTION 10
What is an advantage of implementing a Trusted Platform Module for disk encryption?
A. It provides hardware authentication.
B. It allows the hard disk to be transferred to another device without requiring re- encryption.dis
C. It supports a more complex encryption algorithm than other disk-encryption technologies.
D. It can protect against single points of failure.
Correct Answer: A
Read more: http://www.leads4pass.com/210-260.html Cisco 210-260 Security is the industry leader in information technology, and getting certified by them is a guaranteed way to succeed with IT careers. We help you do exactly that with our high quality Cisco CCNA Security Implementing Cisco Network Security training materials.
Download free Cisco 210-260 pdf files: https://drive.google.com/open?id=0B7LFs7RuvDV4WXRjeWltNnZqUzA