How to Prepare for Cisco 200-201 Exam in 2023?
2023 is a very competitive year. All walks of life and individuals are working hard for their lives, as are professionals engaged in the Cisco industry! Today I am going to introduce the 2023 Cisco 200-201 certification exam!
The Cisco 200-201 exam is a challenging exam designed to test your knowledge of Cisco network security operations fundamentals. If you plan to take the exam, it’s important to be well-prepared.
This article will outline some tips on how to prepare for the Cisco 200-201 exam.
Cisco 200-201 Exam Objectives
The first step in preparing for the Cisco 200-201 exam is to understand the exam objectives. Exam objectives are a list of topics that you will be tested on. To earn the CyberOps Associate certification, you must pass the 200-201 CBROPS exam.
This 120-minute exam tests your knowledge: You can find the exam objectives on the Cisco website.
Cisco 200-201 Exam Prep Package
Below I list exam options that are useful to candidates:
200-201 Exam Books:
Here I recommend two places to get books about the 200-201 exam: (“Cisco CyberOps Associate CBROPS 200-201 Official Cert Guide”, Author: Omar Santos Todd Lammle’s CCNA CyberOps Study Guide) in Amazon and Ciscopress, because they have the highest usage rate, this book involves the content of the exam topic, according to the feedback from netizens, it takes about 1 month to actually complete the study.
200-201 Online Courses:
Online tutorials have been developed over the years to be a more flexible and straightforward learning mode, and there are many well-known platforms online that cover topics covered by the Cisco 200-201 exam.
Some of the most popular online courses include Cisco CyberOps Associate (CBROPS 200-201) on Udemy…
200-201 Practice Exam:
Practice exams are a great way to test your knowledge and prepare for the Cisco 200-201 exam. There are many practice exams available online.
Some of the most popular practice exams include 200-201 dumps on leads4pass: https://www.leads4pass.com/200-201.html (264 Q&A), study plans available in both PDF and VCE formats…
In addition to learning the material, it’s important to experience Cisco equipment first-hand. You can do this by taking a lab class or setting up a lab environment at home.
Best experience sharing:
The best way to prepare for the Cisco 200-201 exam is to practice regularly. This means studying the material, taking practice exams, and gaining practical experience. The more you practice, the better prepared you will be for the exam.
Latest Cisco 200-201 online practice:
| Type | Number of exam questions | Exam name | Exam code | verify answer |
| Free | 15 | Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS) | 200-201 | View |
Question 1:
One of the objectives of information security is to protect the CIA of information and systems. What does the CIA mean in this context?
A. confidentiality, identity, and authorization
B. confidentiality, integrity, and authorization
C. confidentiality, identity, and availability
D. confidentiality, integrity, and availability
Question 2:
Which event artifact is used to identify HTTP GET requests for a specific file?
A. the destination IP address
B. TCP ACK
C. HTTP status code
D. URI
Question 3:
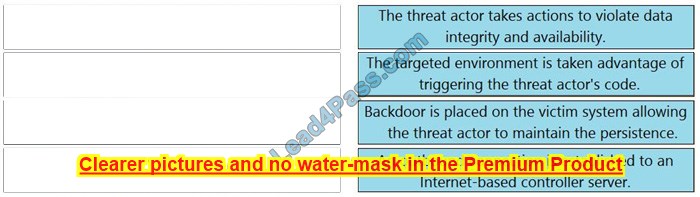
DRAG DROP
Drag and drop the definition from the left onto the phase on the right to classify intrusion events according to the Cyber Kill Chain model.
Select and Place:
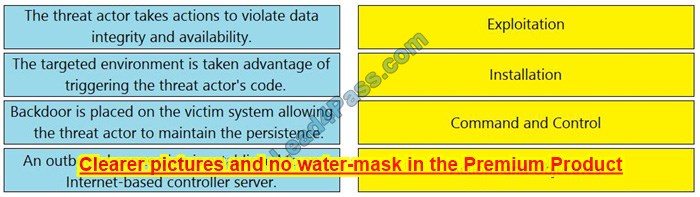
Correct Answer:
Question 4:
An engineer needs to have visibility on TCP bandwidth usage, response time, and latency, combined with deep packet inspection to identify unknown software by its network traffic flow. Which two features of Cisco Application Visibility and Control should the engineer use to accomplish this goal? (Choose two.)
A. management and reporting
B. traffic filtering
C. adaptive AVC
D. metrics collection and exporting
E. application recognition
Question 5:
Refer to the exhibit.

Which type of log is displayed?
A. proxy
B. NetFlow
C. IDS
D. sys
Question 6:
A user received a targeted spear-phishing email and identified it as suspicious before opening the content. To which category of the Cyber Kill Chain model does to this type of event belong?
A. weaponization
B. delivery
C. exploitation
D. reconnaissance
Question 7:
What is the difference between inline traffic interrogation (TAPS) and traffic mirroring (SPAN)?
A. TAPS interrogation is more complex because traffic mirroring applies additional tags to data and SPAN does not alter the integrity and provides a full duplex network.
B. SPAN results in more efficient traffic analysis, and TAPS is considerably slower due to latency caused by mirroring.
C. TAPS replicates the traffic to preserve integrity, and SPAN modifies packets before sending them to other analysis tools
D. SPAN ports filter out physical layer errors, making some types of analyses more difficult, and TAPS receives all packets, including physical errors.
Question 8:
What is the relationship between a vulnerability and a threat?
A. A threat exploits a vulnerability
B. A vulnerability is a calculation of the potential loss caused by a threat
C. A vulnerability exploits a threat
D. A threat is a calculation of the potential loss caused by a vulnerability
Question 9:
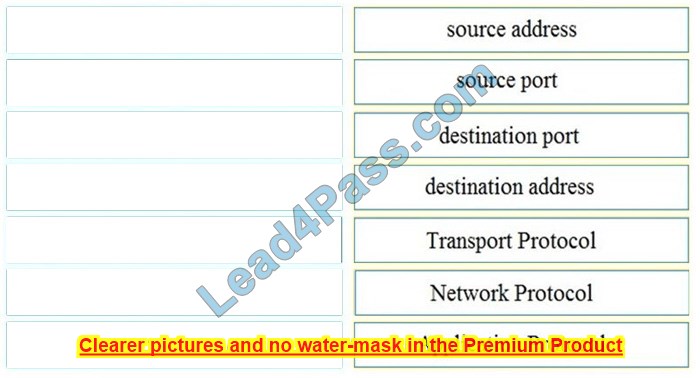
DRAG DROP
Refer to the exhibit. Drag and drop the element name from the left onto the correct piece of the PCAP file on the right.
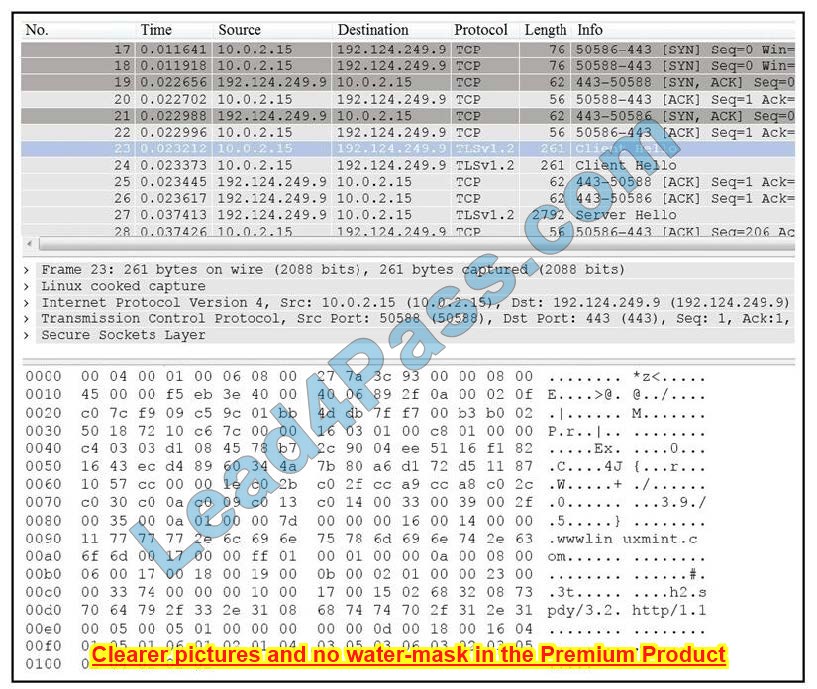
Select and Place:
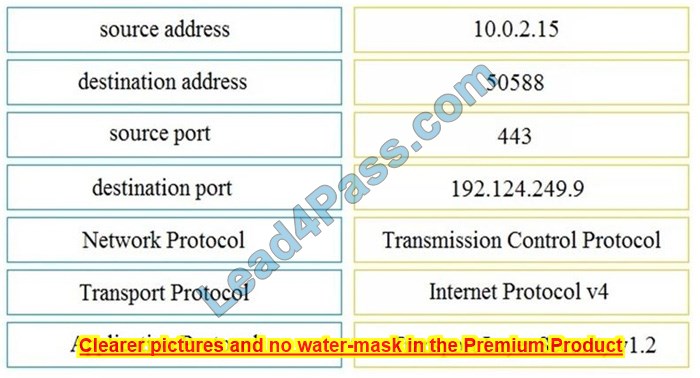
Correct Answer:
Question 10:
An analyst received an alert on their desktop computer showing that an attack was successful on the host. After investigating, the analyst discovered that no mitigation action occurred during the attack. What is the reason for this discrepancy?
A. The computer has HIPS installed on it.
B. The computer has a NIPS installed on it.
C. The computer has HIDS installed on it.
D. The computer has a NIDS installed on it.
Question 11:
Which action should be taken if the system is overwhelmed with alerts when false positives and false negatives are compared?
A. Modify the settings of the intrusion detection system.
B. Design criteria for reviewing alerts.
C. Redefine signature rules.
D. Adjust the alert schedule.
Traditional intrusion detection system (IDS) and intrusion prevention system (IPS) devices need to be tuned to avoid false positives and false negatives. Next-generation IPSs do not need the same level of tuning compared to traditional IPSs.
Also, you can obtain much deeper reports and functionality, including advanced malware protection and retrospective analysis to see what happened after an attack took place.
Ref: Cisco CyberOps Associate CBROPS 200-201 Official Cert Guide
Question 12:
What is the difference between mandatory access control (MAC) and discretionary access control (DAC)?
A. MAC is controlled by the discretion of the owner and DAC is controlled by an administrator
B. MAC is the strictest of all levels of control and DAC is object-based access
C. DAC is controlled by the operating system and MAC is controlled by an administrator
D. DAC is the strictest of all levels of control and MAC is object-based access
Question 13:
During which phase of the forensic process are tools and techniques used to extract information from the collected data?
A. investigation
B. examination
C. reporting
D. collection
Question 14:
Refer to the exhibit.
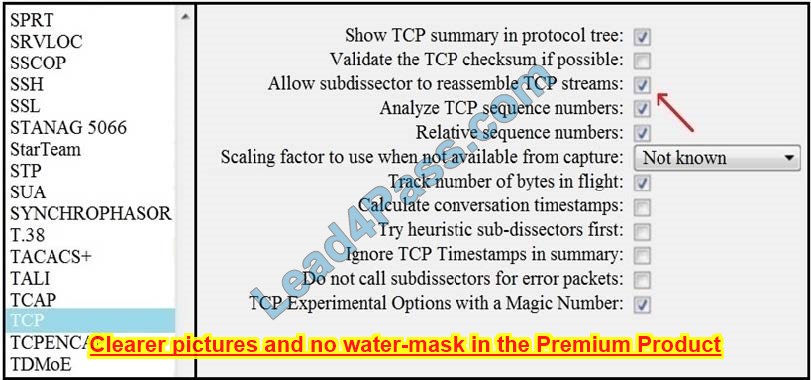
What is the expected result when the “Allow sub-dissector to reassemble TCP streams” feature is enabled?
A. insert TCP sub-dissectors
B. extract a file from a packet capture
C. disable TCP streams
D. unfragmented TCP
Question 15:
What ate the two categories of DDoS attacks? (Choose two.)
A. split-brain
B. scanning
C. phishing
D. reflected
E. direct
Verify answer:
| Number: | Q1 | Q2 | Q3 | Q4 | Q5 | Q6 | Q7 | Q8 | Q9 | Q10 | Q11 | Q12 | Q13 | Q14 | Q15 |
| Answers: | D | D | IMAGE | AE | B | B | D | A | IMAGE | C | A | B | D | D | DE |
The above practice questions are from some leads4pass 200-201 dumps, click on the link: https://www.leads4pass.com/200-201.html, and use the complete exam practice questions to help you pass the exam 100%.
To take the 200-201 exam
Once you are confident that you are ready for the test, you can schedule the test. You can take the exam at a Pearson VUE testing center.
Pass the exam
The passing score for the Cisco 200-201 exam is 1000 out of 1500. If you pass the exam, you will earn the Cisco Certified CyberOps Associate certification.
In conclusion
The Cisco 200-201 exam is a challenging exam, but possible with hard work and preparation. If you follow the tips in this article, you will successfully pass the Cisco 200-201 exam and earn the Cisco Certified CyberOps Associate certification.
Thanks to my assistant: Google Bard
![[New May 2023] Updated 300-425 Dumps For 300-425 ENWLSD Exam](https://www.ciscoexampdf.com/wp-content/uploads/2023/05/Updated-300-425-Dumps.jpg)